How do you find the cipher of a number?
How do you find the cipher of a number?
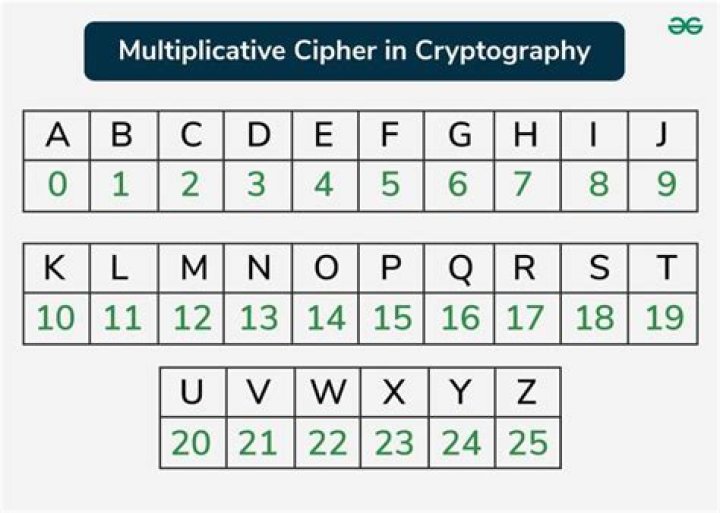
Letter Number (A1Z26) A=1, B=2, C=3. Tool to convert letters to numbers and vice versa. The Letter-to-Number Cipher (or Number-to-Letter Cipher) consists in replacing each letter by its position in the alphabet, for example A=1, B=2, Z=26, hence its over name A1Z26.
How do you use a cipher wheel with numbers?
Look at your coded message, each letter can be found on the inside wheel. Write down the corresponding letter from the outside wheel (the letter that is right above the letter from the message). Repeat this for the rest of the coded message and you will reveal the secret information or phrase.
What is the cipher code?
Cipher — A cipher is a system to make a word or message secret by changing or rearranging the letters in the message. Example: For example: A=G or A=&. Code — A code is a system of changing entire words or phrases into something else. Codes are not.
How do you decode a cipher with a key?
Example: To decrypt NGMNI, the key is KEY and the alphabet is ABCDEFGHIJKLMNOPQRSTUVWXYZ. To decrypt, take the first letter of the ciphertext and the first letter of the key, and subtract their value (letters have a value equal to their position in the alphabet starting from 0).
What is a Gronsfeld cipher?
The Gronsfeld cipher is a polyalphabetic substitution cipher, whereby plaintext letters are shifted by a number of places in the alphabet according to digits in a key number (like a PIN).
What is Bill cipher wheel?
The Zodiac is a symbol associated with Bill Cipher and the symbols surrounding him. It is later revealed that this wheel is a prophecy that can be used to defeat him.
What is the most difficult code to break?
Here are 5 of the world’s hardest codes to crack
- Rosetta Stone. The Rosetta Stone dates back to 196 BC, but in the modern day we rediscovered it in 1799 – inscribed in three different scripts, it provided an excellent puzzle for archaeologists.
- Voynich manuscript.
- Phaistos Disc.
- The Shugborough Inscription.
- Mayan script.
Can you decrypt without key?
No, not with the current hardware if a good encryption method was used and the key (password) was long enough. Unless there is a flaw in the algorithm and that you know it, your only option is to brute force it which might takes hundred of years.
How do I read an encrypted message?
How to Read Encrypted Text Messages Through Textpad
- Launch TextPad and open the encrypted message in the program.
- Select the entire text of the message by pressing the “Ctrl-A” keys.
- Open the appropriate encryption software.
- Enter the passphrase or password that was originally used to encrypt the message.
Which is the best way to solve a numbered key cipher?
In solving, it is quite helpful to be able to estimate the length of the extended key and the number of residual alphabetic letters.
How to calculate the length of a cipher?
In this application, N equals the key length, B (N) equals the number of residual letters, and N + B (N) is the length of the extended plaintext alphabet. For example, the crypt, NK-2, in ” The Numbered Key Cipher ” article, the length of the keyed alphabet is by implication 57 — the largest number is 56 and adding one for the 00 gives 57.
How can you tell the Order of letters in a cipher?
Because of the low frequency of most all of the residual letters one can often spot their location in the number sequence, and because they are in alphabetical order and only have one substitute, one may make good guesses on individual residual letters by frequency matching.
How many keys are in a substitution cipher?
For a simple substitution cipher, the set of all possible keys is the set of all possible permutations. Thus, for the English alphabet, the number of keys is 26! (factorial of 26), which is about . Because of this, if you want to decipher the text without knowing the key, the brute force approach is out of the question.
Is it possible to solve a number Cypher?
That means solving a cypher is usually a matter of looking for high frequency letters and taking educated guesses. Solving number cyphers is possible, but time consuming: it requires a great deal of patience, especially with ciphers under 200 words. Count how many times each number appears in your cipher. You may be able to spot patterns.
Are there different ways to encode a book cipher?
There is no need in a book cipher to keep using the same location for a word or letter. On the contrary, it is more secure to encode it in different ways. An Ottendorf cipher is a book cipher consisting of three parts. Usually in one of these formats: page number – word number – letter number line number – word number – letter number
In this application, N equals the key length, B (N) equals the number of residual letters, and N + B (N) is the length of the extended plaintext alphabet. For example, the crypt, NK-2, in ” The Numbered Key Cipher ” article, the length of the keyed alphabet is by implication 57 — the largest number is 56 and adding one for the 00 gives 57.
Because of the low frequency of most all of the residual letters one can often spot their location in the number sequence, and because they are in alphabetical order and only have one substitute, one may make good guesses on individual residual letters by frequency matching.