What is Cybermap Kaspersky?
What is Cybermap Kaspersky?
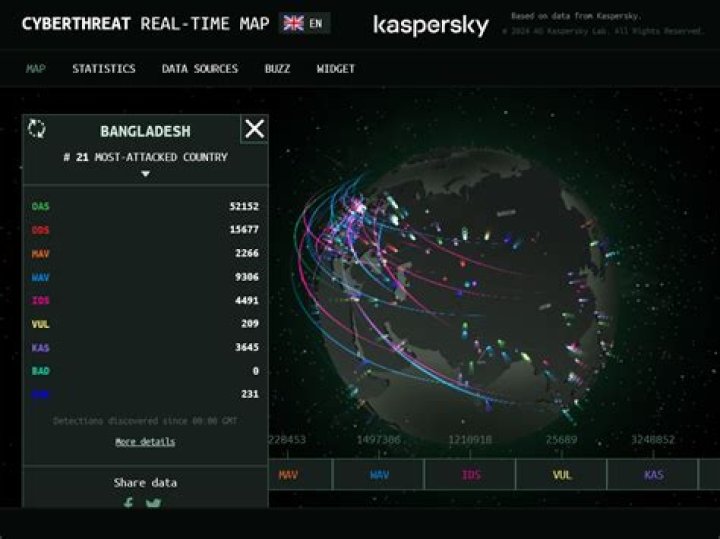
Kaspersky Lab presents its new interactive Cyberthreats Realtime Map. Living up to its name, this visual tool allows users to see what is going on in cybersecurity around the world in real time. Data from KSN allows Kaspersky Lab’s researchers to identify the most vulnerable and most attacked software.
What is a cyber attack map?
Threat maps illustrate the millions of cyber threats happening every day. In addition to visualizing the attacks, cyber threat maps also provide a limited amount of context including the source and target countries, attack types, and historical and (near) real-time data about threats.
What is an OAS attack?
The Organisation Armée Secrète or OAS (meaning Secret Armed Organisation) was a far-right French dissident paramilitary organisation during the Algerian War. The OAS carried out terrorist attacks, including bombings and assassinations, in an attempt to prevent Algeria’s independence from French colonial rule.
What are the top 3 targeted industries?
Per Industry Breakdown
- Energy.
- Retail.
- Professional Services.
- Government.
- Health Care.
- Media and Information Communications.
- Transportation.
- Education. Half (50%) of the attacks on education in 2020 were spam or adware; 10% of attacks were ransomware.
What does DDoS stand for?
Distributed Denial of Service
DDoS stands for Distributed Denial of Service, and it’s a method where cybercriminals flood a network with so much malicious traffic that it cannot operate or communicate as it normally would. This causes the site’s normal traffic, also known as legitimate packets, to come to a halt.
What does a botnet do?
A botnet is a collection of internet-connected devices infected by malware that allow hackers to control them. Cyber criminals use botnets to instigate botnet attacks, which include malicious activities such as credentials leaks, unauthorized access, data theft and DDoS attacks.
How can I tell if I am being Ddosed?
Generally, the best way to examine a potential DDoS attack is through analytic tools. Check to see if a specific traffic source continues to query a certain set of data long after the Time To Live (TTL) for the site has elapsed.
Is DDoS illegal?
For example, a DDoS attack may constitute a federal criminal offense under the Computer Fraud and Abuse Act, a trespass to chattel, or a breach of contract if it violates a website owner’s or internet service provider’s terms of use.
Can OAS go away?
There is no reason to avoid cooked, canned, or processed forms of the foods that do not cause symptoms. Usually, OAS symptoms affecting the mouth and throat are mild, resolve quickly, and do not need treatment. However, more severe symptoms may occur rarely.
Is OAS dangerous?
Rarely, OAS can cause severe throat swelling leading to difficulty swallowing or breathing. In a person who is highly allergic, a systemic reaction, called anaphylaxis (an-a-fi-LAK-sis), may be caused by a pollen cross-reactive raw fruit or vegetable, but this is very uncommon. OAS can occur at any time of the year.
Who is most at risk for cyber attacks?
The industries most vulnerable to cyber attacks:
- Small businesses.
- Healthcare institutions.
- Government agencies.
- Energy companies.
- Higher education facilities.
Who do hackers target the most?
Small and medium business are the top target for cyberattacks. Unlike large corporations who have the money and resources to pay for cybersecurity and upgrade their network match the latest hacker tricks, small businesses do not have that same luxury” and hackers know it.
What’s the purpose of a cyber attack map?
What’s a cyber attack map? A cyber attack map is just a fancy, graphical way to show how the Internet works. Day by day, millions of cyber threats hit new victims; some of them performing counter attack, others mitigating the attacks and remaining passive.
Are there any real time cyber threat maps?
A cyber threat map, also known as a cyber attack map, is a real-time map of the computer security attacks that are going on at any given time. One of the most famous was released by the company Norse and went so viral, even among non-hackers, that it got its own story in Newsweek in 2015.
Are there any live maps of cyber attacks?
They are wrongly advertised as “live maps”—most do not show live attack data, but records of past attacks. They are focused on showing Distributed Denial of Service (DDoS) attacks only, and not other types of cybercrime. They only show anonymous traffic data.
Is the Kaspersky cyber attack map real time?
The attacks shown on the Kaspersky map are taken from on-demand and on-access scans, as well as web and email detections. But it isn’t clear just how real-time, the real-time presentation is. Fortinet’s cyber attack map looks similar to the one from Norse and appears to show a playback of recorded events.
What’s a cyber attack map? A cyber attack map is just a fancy, graphical way to show how the Internet works. Day by day, millions of cyber threats hit new victims; some of them performing counter attack, others mitigating the attacks and remaining passive.
A cyber threat map, also known as a cyber attack map, is a real-time map of the computer security attacks that are going on at any given time. One of the most famous was released by the company Norse and went so viral, even among non-hackers, that it got its own story in Newsweek in 2015.
They are wrongly advertised as “live maps”—most do not show live attack data, but records of past attacks. They are focused on showing Distributed Denial of Service (DDoS) attacks only, and not other types of cybercrime. They only show anonymous traffic data.
The attacks shown on the Kaspersky map are taken from on-demand and on-access scans, as well as web and email detections. But it isn’t clear just how real-time, the real-time presentation is. Fortinet’s cyber attack map looks similar to the one from Norse and appears to show a playback of recorded events.