What is endpoint detection
Share: Endpoint detection and response (EDR), also known as endpoint threat detection and response (ETDR), is an integrated endpoint security solution that combines real-time continuous monitoring and collection of endpoint data with rules-based automated response and analysis capabilities.
What is endpoint threat detection?
Share: Endpoint detection and response (EDR), also known as endpoint threat detection and response (ETDR), is an integrated endpoint security solution that combines real-time continuous monitoring and collection of endpoint data with rules-based automated response and analysis capabilities.
How does end point detection work?
How Endpoint Detection and Response Works. Endpoint detection and response tools work by monitoring endpoint and network events and recording the information in a central database where further analysis, detection, investigation, reporting, and alerting take place.
What is an endpoint detection tool?
Endpoint Detection and Response (EDR), also referred to as endpoint detection and threat response (EDTR), is an endpoint security solution that continuously monitors end-user devices to detect and respond to cyber threats like ransomware and malware.Why do I need endpoint detection and response?
Why Is EDR Important? Compared to traditional security solutions, EDR provides enhanced visibility into your endpoints and allows for faster response time. Furthermore, EDR tools detect and protect your organization from advanced forms of malware (such as polymorphic malware), APTs, phishing, etc.
What is advanced endpoint detection?
Advanced endpoint protection protects systems from file, fileless, script-based and zero-day threats by using machine-learning or behavioral analysis. Traditional, reactive endpoint security tools such as firewalls and anti-virus software generally depend upon known threat information to detect attacks.
What is EDP and EDR?
‘EPP (Endpoint Protection Platform) covers traditional anti-malware scanning, whereas EDR (Endpoint Detection and Response) covers some more advanced capabilities like detecting and investigating security incidents, and ability to remediate endpoints to pre-infection state.
What is CrowdStrike company?
CrowdStrike, Inc. provides cyber security products and services. The Company offers endpoint protection and threat intelligence solutions that enables customers to prevent damage from targeted attacks, detect and attribute advanced malware, and search all endpoints. CrowdStrike serves customers worldwide.What does CrowdStrike Falcon do?
Falcon is the CrowdStrike platform purpose-built to stop breaches via a unified set of cloud-delivered technologies that prevent all types of attacks — including malware and much more.
What is Microsoft Defender for endpoint?Microsoft Defender for Endpoint is an enterprise endpoint security platform designed to help enterprise networks prevent, detect, investigate, and respond to advanced threats.
Article first time published onWhat are endpoint attacks?
Endpoint attacks target user systems rather than their servers. These user systems are entry points to network and include smartphones, computers, laptops and fixed-function devices. Endpoint attacks also affect the shared folders, network-attached storage (NAS) and hardware such as server systems.
How do you create an endpoint detection and response?
Create EDR policies. Sign in to the Microsoft Endpoint Manager admin center. Select Endpoint security > Endpoint detection and response > Create Policy. Select the platform and profile for your policy.
When did endpoint detection and response come out?
Endpoint detection and response first emerged in 2013 to help forensic investigations that required very detailed endpoint telemetry to analyze malware and understand exactly what an attacker did to a compromised device.
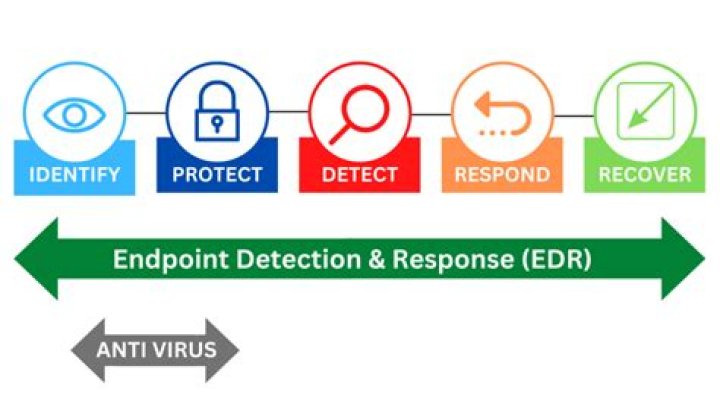
What is the difference between EDR and antivirus?
Antivirus can be perceived as a part of the EDR system. … EDR security system, on the other hand, serves a much larger role. EDR not only includes antivirus, but it also contains many security tools like firewall, whitelisting tools, monitoring tools, etc. to provide comprehensive protection against digital threats.
Is McAfee ePO an EDR?
McAfee ePO manages MVISION EDR extensions to communicate with the DXL Broker and MVISION EDR cloud services. The DXL Broker is a communication fabric among MVISION EDR services, the cloud, and devices.
What is EPP in cyber security?
An endpoint protection platform (EPP) is a solution deployed on endpoint devices to prevent file-based malware attacks, detect malicious activity, and provide the investigation and remediation capabilities needed to respond to dynamic security incidents and alerts.
What is XDR in cyber security?
According to analyst firm Gartner, Extended Detection and Response (XDR) is “a SaaS-based, vendor-specific, security threat detection and incident response tool that natively integrates multiple security products into a cohesive security operations system that unifies all licensed components.”
What is next generation endpoint security?
Share: Next-generation endpoint security uses modern artificial intelligence (AI), machine learning, and a tighter integration of network and device security to provide more comprehensive and adaptive protection than traditional endpoint security solutions.
What is EDR and MDR?
MDR stands for managed detection and response. MDR is a service that continuously monitors, prioritizes, and responds to cybersecurity threats with humans behind the wheel. MDR is augmented with EDR solutions by empowering analysts with data and abilities to act on the endpoint.
What is endpoint application isolation and containment technology?
Endpoint application isolation and containment technology is a form of zero-trust endpoint security. Instead of detecting or reacting to threats, it enforces controls that block and restrain harmful actions to prevent compromise.
What is CrowdStrike OverWatch?
CrowdStrike Falcon OverWatch™ is a managed hunting service responsible for detecting intrusions, malicious activities and adversaries that may otherwise go undetected.
What is a CID in Falcon?
The CrowdStrike Customer Identification (CID) is used to: Activate the CrowdStrike Falcon Sensor. Troubleshoot the CrowdStrike Falcon Console.
Does Dell own CrowdStrike?
Customers who have purchased CrowdStrike through Dell may get support by contacting: United States (US): Dell Data Security ProSupport at 877.459.
What is Endpoint Security CrowdStrike?
Endpoint security, or endpoint protection, is the cybersecurity approach to defending endpoints – such as desktops, laptops, and mobile devices – from malicious activity.
What is Darktrace used for?
Darktrace AI interrupts in-progress cyber-attacks in seconds, including ransomware, email phishing, and threats to cloud environments and critical infrastructure. Join over 5,500 organizations worldwide that rely on a digital immune system to avoid cyber disruptions, without impacting regular business operations.
What is CrowdStrike mission?
Our mission is to stop breaches and our purpose is a promise: to provide safety and security to some of the world’s largest, most influential companies and, by extension, the billions of people around the world who use their services.
Is Microsoft Defender for endpoint good?
Not only is Microsoft Defender Antivirus an excellent next-generation antivirus solution, but combined with other Defender for Endpoint capabilities, such as endpoint detection and response and automated investigation and remediation, you get better protection that’s coordinated across products and services.
Is defender good enough?
Microsoft’s Defender is pretty good at detecting malware files, blocking exploits and network-based attacks, and flagging phishing sites. It even includes simple PC performance and health reports as well as parental controls with content filtering, usage limitations, and location tracking.
Is Microsoft Defender for endpoint free?
Microsoft Defender for Endpoint offers a free trial and several different pricing plans from $10 per user per month up to $57 per user per month. For more information, visit
What is an example of an endpoint?
An endpoint is any device that is physically an end point on a network. Laptops, desktops, mobile phones, tablets, servers, and virtual environments can all be considered endpoints. When one considers a traditional home antivirus, the desktop, laptop, or smartphone that antivirus is installed on is the endpoint.
What does endpoint mean?
Definition of end point 1 : a point marking the completion of a process or stage of a process especially : a point in a titration at which a definite effect (such as a color change) is observed.



